This is a follow-up post from building a lab for malware analysis that you can apply to decrypt the malware HTTPS traffic from REMnux.
PolarProxy is a transparent SSL/TLS proxy designed to intercept and decrypt TLS traffic, and save it in PCAP format so that we can analyze it further using Wireshark. PolarProxy is also installed by default in REMnux.
VM Configuration
REMnux
PolarProxy will listen on port 10443, for that we have to redirect traffic 443 to 10443. To do this we have to create some iptables rules. ens37 here is my Host-only interface, you can customize it yourself:
sudo iptables -A INPUT -i ens37 -p tcp --dport 10443 -m state --state NEW -j ACCEPT
sudo iptables -t nat -A PREROUTING -i ens37 -p tcp --dport 443 -j REDIRECT --to 10443After the rule is created, to run PolarProxy you can use the following command:
sudo polarproxy -v -p 10443,80,443 --certhttp 10080 -w ~/polarproxy.pcapYou can customize the destination PCAP file location, in this case I saved it in the user directory named polarproxy.pcap.
Windows
Next, you need to install the root CA certificate from PolarProxy on your Windows VM. For that you have to download the certificate file first by visiting the following REMnux VM address, for example in my case: http://192.168.126.100:10080/, then the polarproxy.cer file will be downloaded automatically.
Windows:
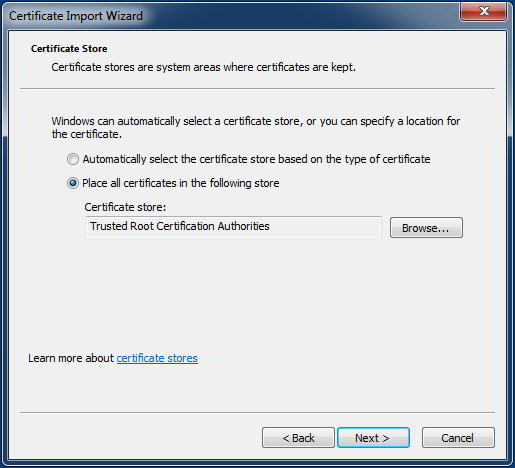
- Double click the
polarproxy.cerfile and click [Install Certificate…] - Click [Next] and then select “Place all certificates in the following store“
- Click [Browse] and select “Trusted Root Certification Authorities” and click [OK]
- Click [Next] and [Finish]
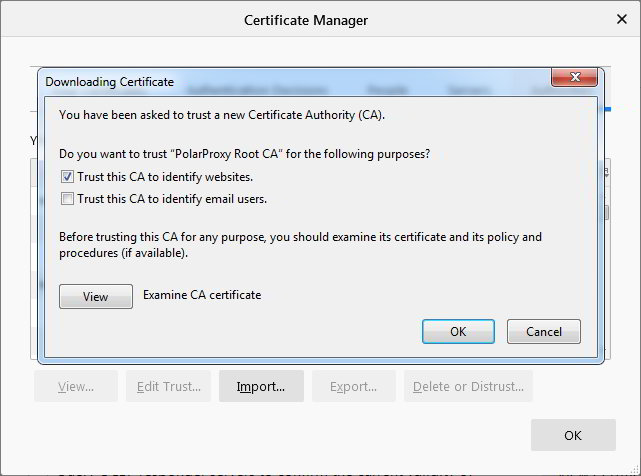
Firefox:
- Go to [Options > Privacy & Security]
- In the Certificates section, click [View Certificates…]
- On the Authorities tab, click the [Import…] button and select the
polarproxy.cerfile - Check “Trust this CA to identify websites” and click [OK]
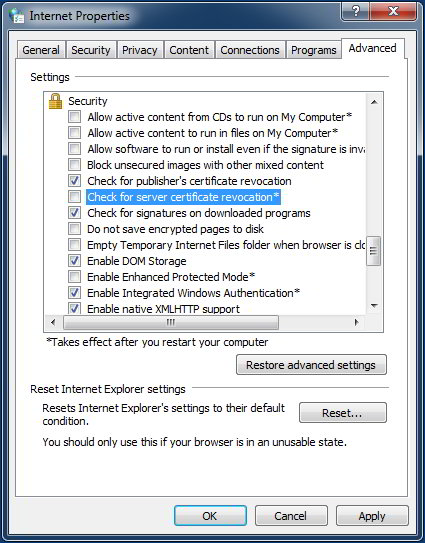
Additionally we can disable the certificate revocation check:
- In the Run box execute the following command:
inetcpl.cpl - Click the tab [Advanced] and scroll to the bottom named [Security]
- Uncheck the “Check for server certificate revocation” then click [OK]
- And restart the VM.
If everything is running smoothly, now you can create a snapshot of the VM. Configuration on this VM can also be applied to your other VMs.